
A full overview of all Microsoft 365 (Business, F1, E3 and E5) plans and their features in a table for your convenience 🙂

A full overview of all Microsoft 365 (Business, F1, E3 and E5) plans and their features in a table for your convenience 🙂
Often we, as cloud admins, need our audit or sign in logs. Usually, we need real-time data because, for example, we’re debugging why that one user has conditional access issues. But sometimes, we need to go back further than 30 days. And that is not something Azure does by default, but can be enabled:
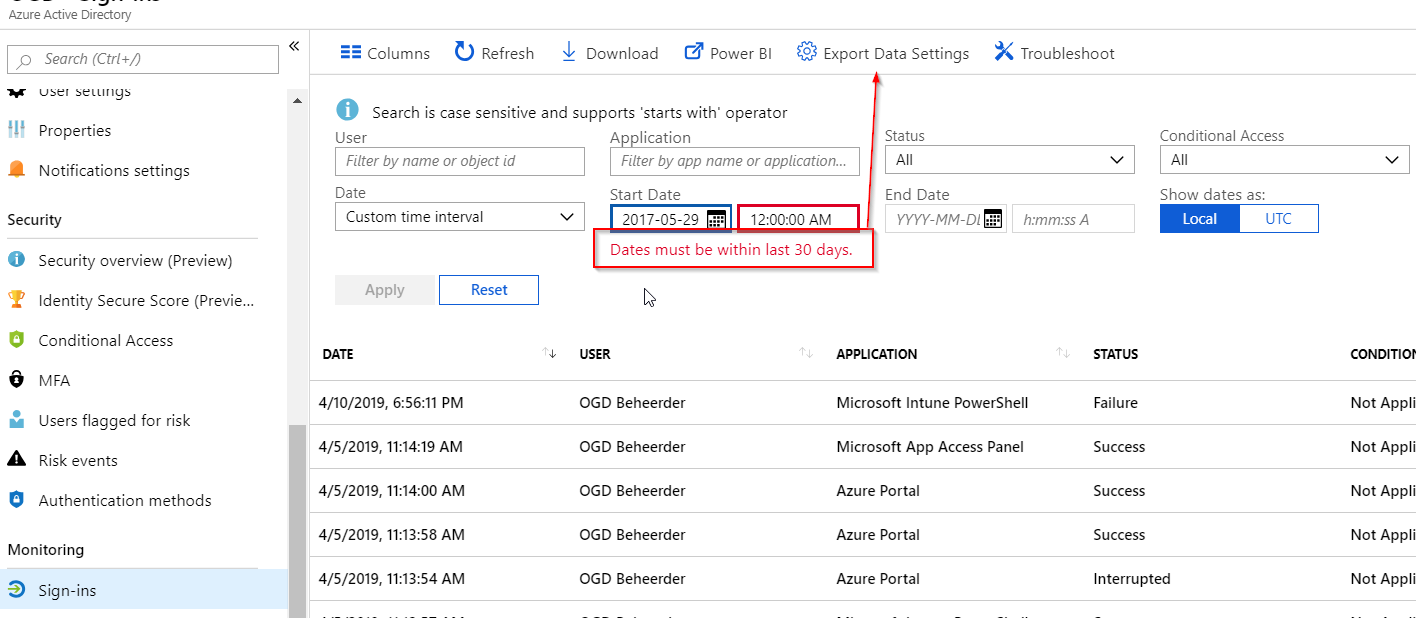
Our options when exporting logs are limited to a Storage account, Log Analytics or an Event Hub. All these options offer multiple extraction methods to cover your transport needs to other systems. The default retention period is then forever, which is nice as we might need audit info going back a bit as hacks are usually discovered after about 206 days.
If you don’t have specific tools or requirements, I recommend setting up a Log Analytics workspace and connecting that to Azure AD:
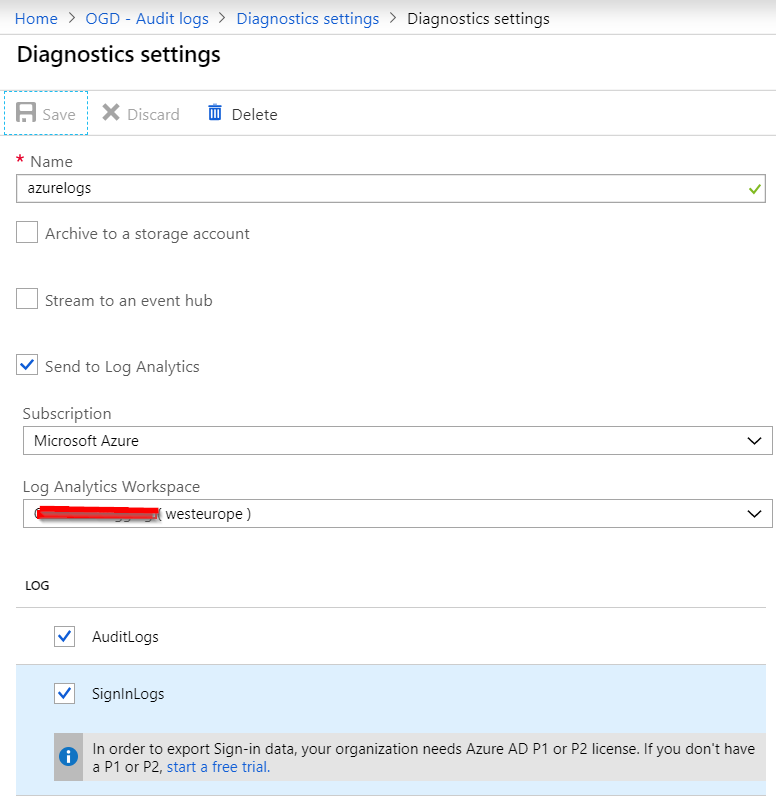
Whichever method you choose, a P1 or P2 license is required. You only need a single license for the entire tenant when using the export audit / singin log functionality of AzureAD. Once configured, the Logs option directly bring you to the Log Analytics workspace search results:
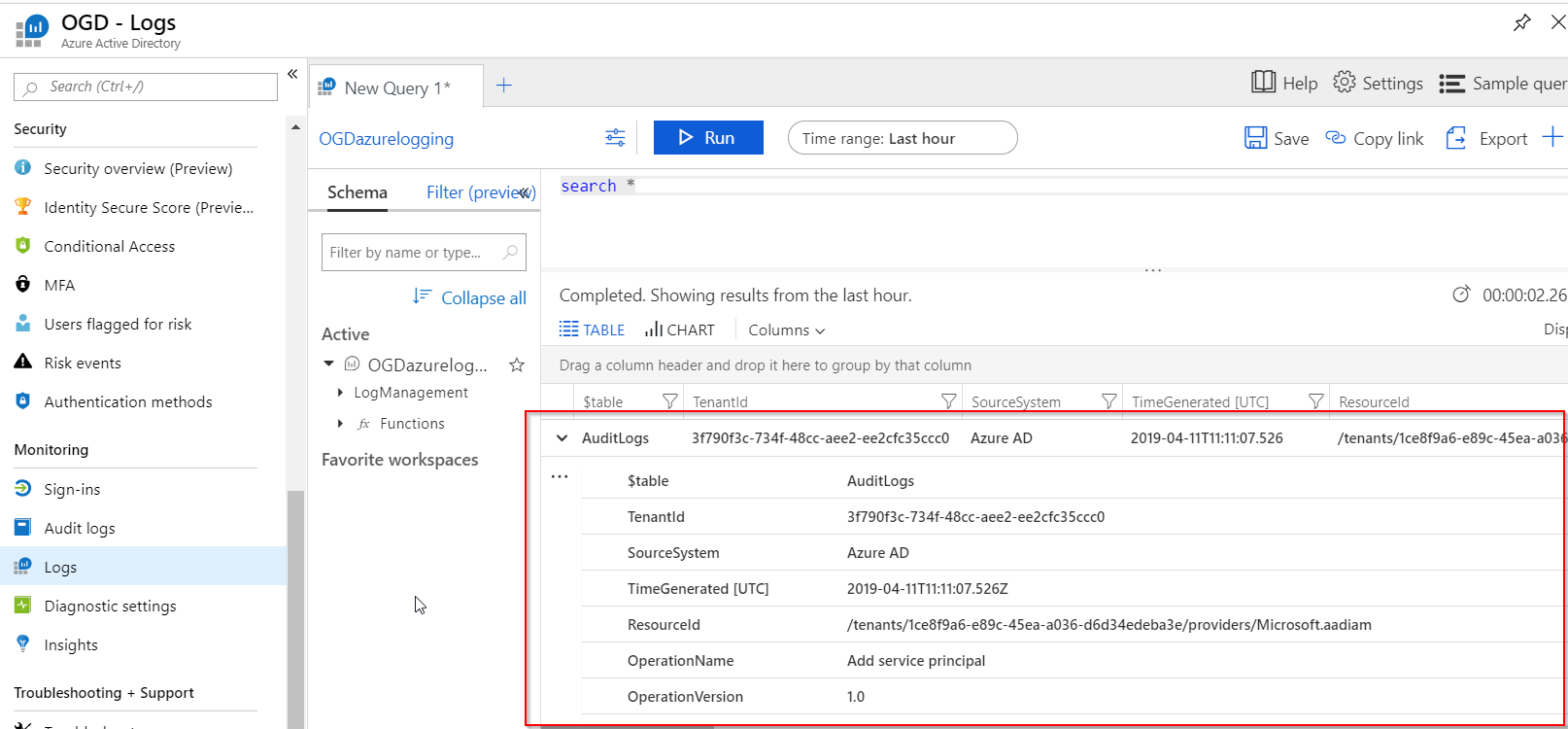
I’ve briefly shown how to configure AzureAD to send audit and sign in logs to Log Analytics so you can go back further than 30 days. Stay tuned for the next post that will utilize these logs to dive deeper into Guest User activity.
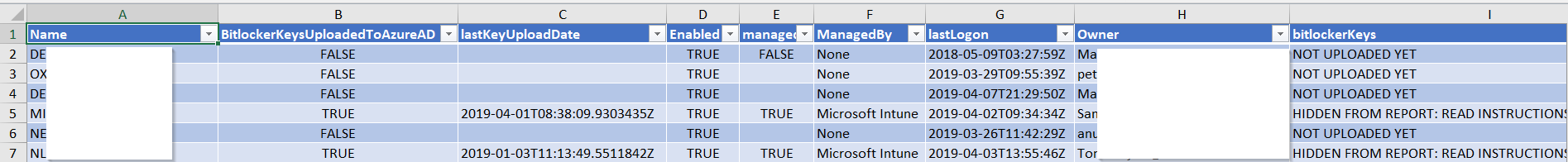
With Intune’s new Bitlocker Encryption Report administrators have an effective way of seeing which of their devices have been encrypted.
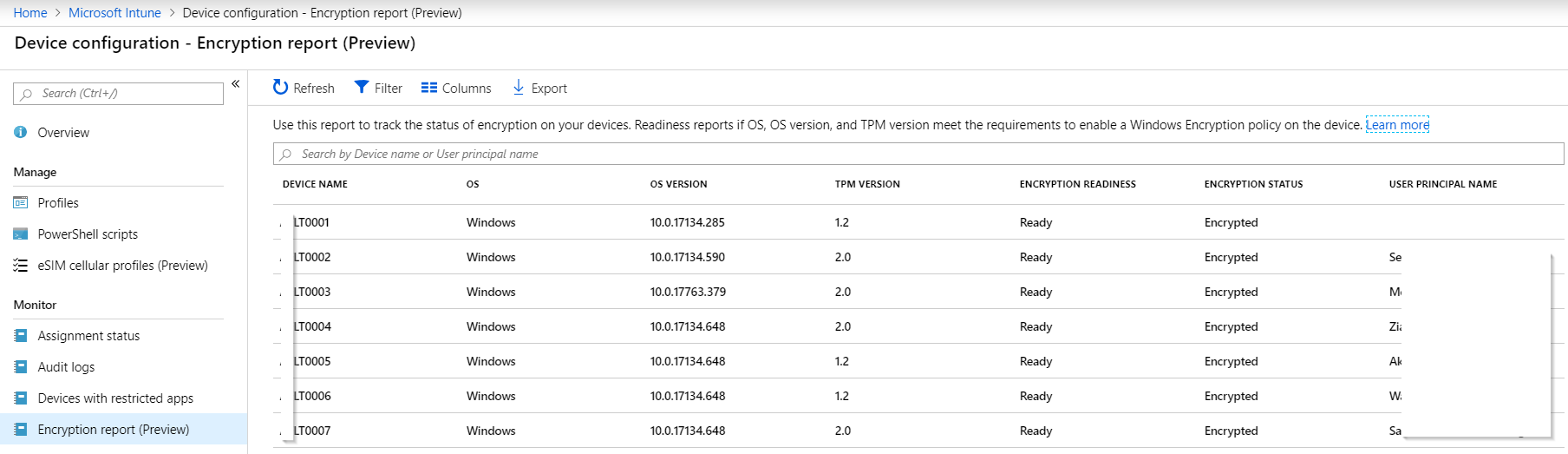
But if we want to know if we can actually recover the bitlocker key of a device, we need to know if it was ever uploaded to AzureAD.
Network or local device issues can sometimes prevent the recovery key from reaching AzureAD, resulting in lost data if the device’s disk needs to be recovered for any reason. To hunt down devices that have not escrowed their recovery key to AzureAD, you can use my report function (in PowerShell as always):
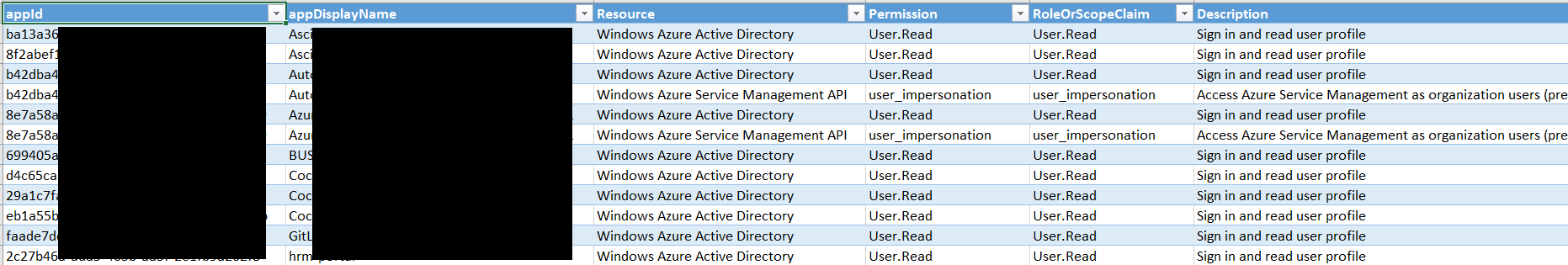
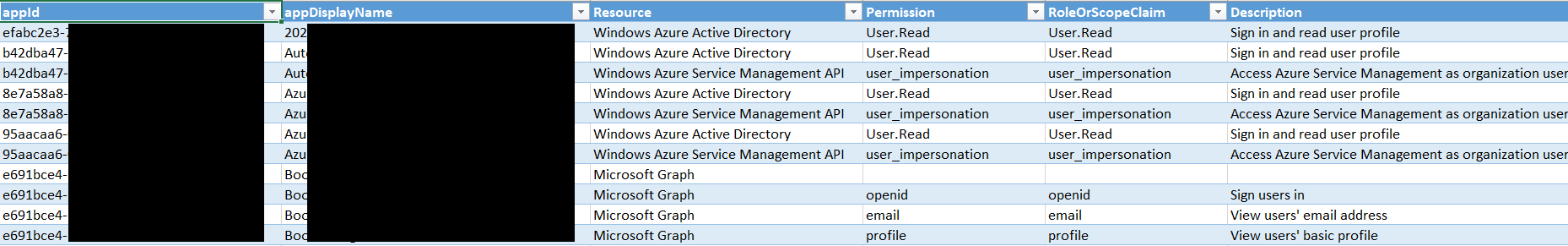
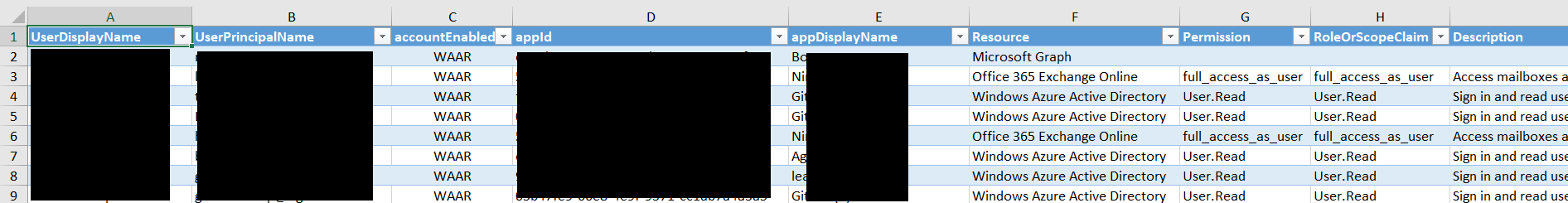
So you’d like to know which applications are living in your AzureAD?
And you’d like to know which of those were added by your admins, and what permissions those applications have?
And you’d also like to know which applications your users are consenting to, and what rights those applications have on your users?
Look no further, I wrote a script to export all of that to Excel for you!
Apps an admin has consented to and the type of rights it needs
Apps a user has consented to and the type of rights it needs
Apps to user mapping, for an easy overview of which user has consented to which app
Get it at:
Credits to Doug Finke for the Excel module I’m using!
The Microsoft supplied Get-AzureRMADApplication Powershell cmdlet does not return all applications you can see in the Enterprise Applications and App registrations blades in Azure AD.
In addition, Get-AzureRmAdApplication also does not return information such as:
So, here’s a custom PS function to help you out: https://gitlab.com/Lieben/assortedFunctions/blob/master/get-azureRMADAllApplications.ps1
It requires a special token generated by my get-AzureRMtoken function to log in.
As usual when using unsupported API’s, be careful!