Azure AD, Intune and Windows 10 offer an incredibly nice light management option, where your users can use any Windows 10 Pro or higher device and simply join it to your Azure AD on their own.
Intune then allows you to enforce your security policies on those devices, and to distribute AppX and MSI packages to those devices.
Traditionally, IT used to manage devices using GPO’s or more, allowing a very high degree of granular configuration and remediation. Intune or the Enterprise Mobility Suite don’t offer good alternatives for Group Policy, and don’t allow scripts to be deployed natively, this greatly limits us.
However, the ability to deploy an MSI can be leveraged to still offer any of the granular management we used to do. I would very, very strongly advocate only using this as a last resort, don’t swim against the current, let users manage their own device and move to a services based architecture for your organisation’s IT.
Today’s case for a global NGO with a fully EMS licensed user base covers the distribution and installation of a large number of templates for Microsoft Word, including a normal.dot, macro’s and the required group policy settings to make word use these templates.
Requirements:
- A test user with an EMS licence (or seperate Azure AD Premium and Intune)
- Source files
- Advanced Installer (free license)
Steps:
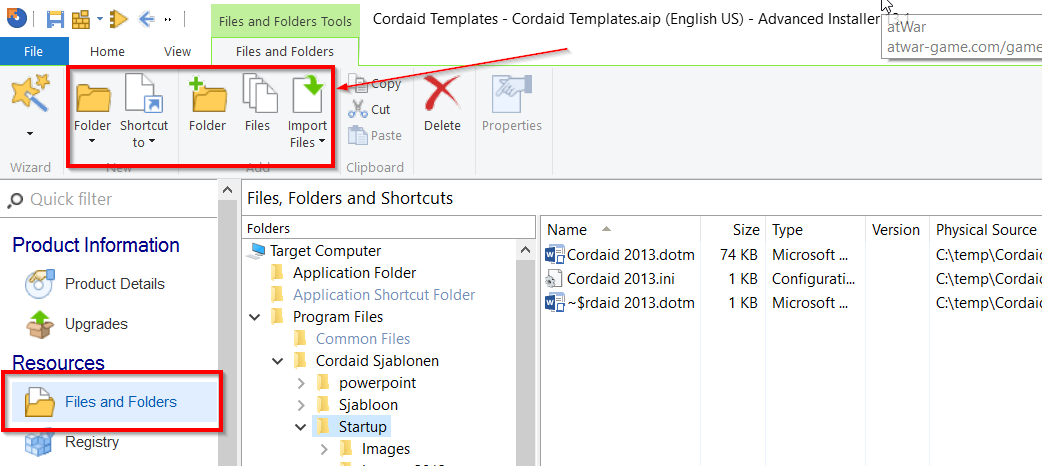
First, let’s start a ‘Simple’ project in Advanced Installer, this does not require a license, and drag your files into a new folder under Program Files in the Files and Folders menu:
These will then end up in the c:\program files (x86)\<chosen foldername> location on the target client.
Searching for the right registry keys corresponding to a GPO setting?
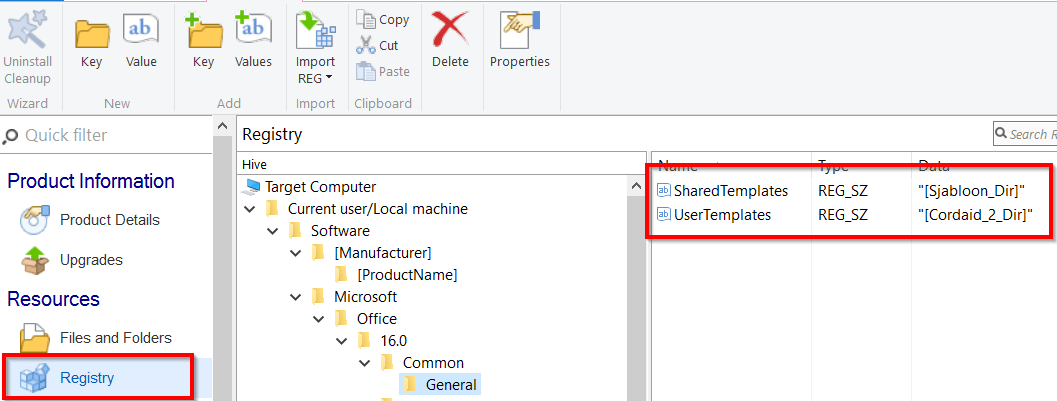
Now create registry keys under the correct Office registry branch (16.0 for Office 2016) to direct Office to the right location. SharedTemplates should point to the folder where your company templates exist. UserTemplates should point to a folder where the user has write-access, usually somewhere in AppData.
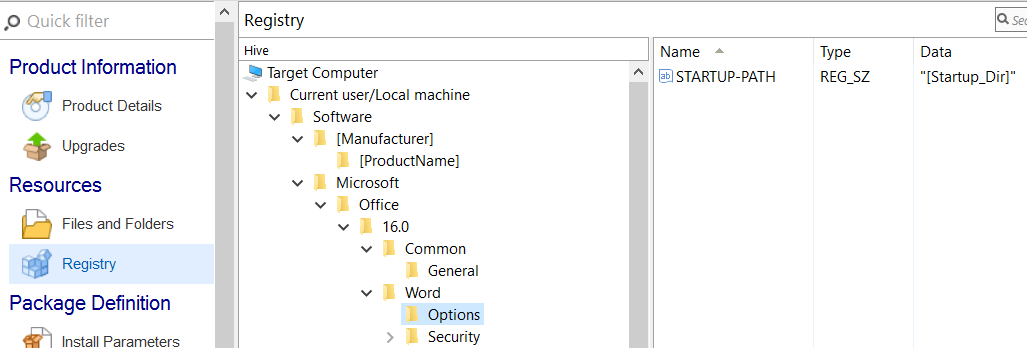
My templates have a so called startup folder, if you point word to this folder Word will load all templates in there, our most important one was a normal.dot containing a selector macro, lets set the registry key for that:
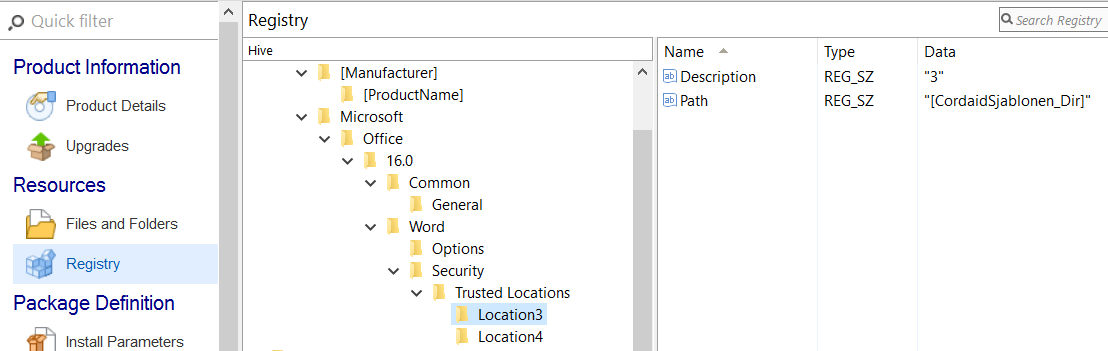
And don’t forget to add a few keys to ensure the locations we’ll be making word access are trusted locations:
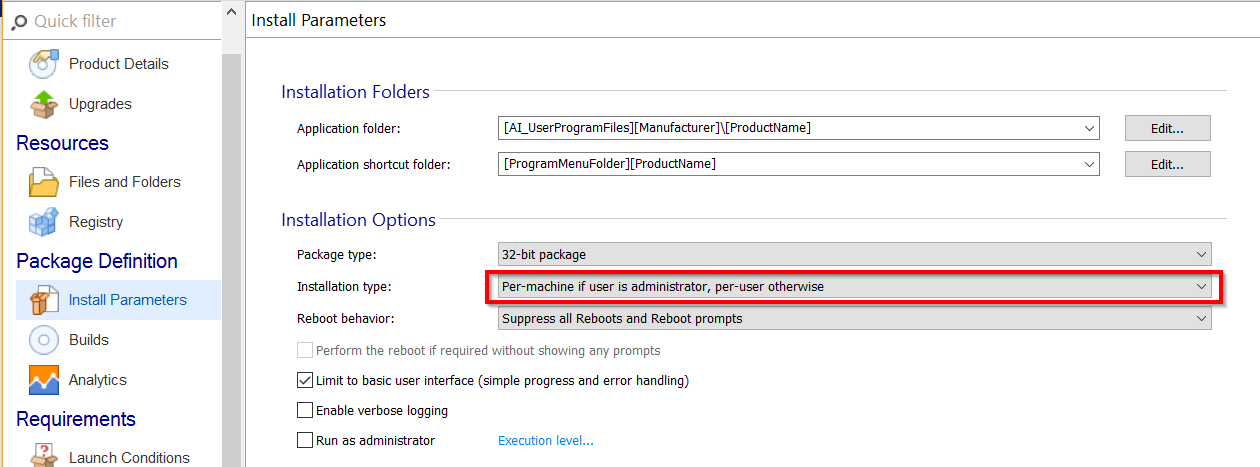
Now that our files and settings are configured, we’ll set the Build Parameter to “Per machine if user is administrator, per user otherwise”. This is the first requirement that will cause the registry keys to end up in the right location (HKCU):
Now just press the build button in the top left and you’ll end up with a single, clean and working MSI file. Log in to the Intune console, and go to the Apps section.
Click Add Apps and load the on demand configuration tool:
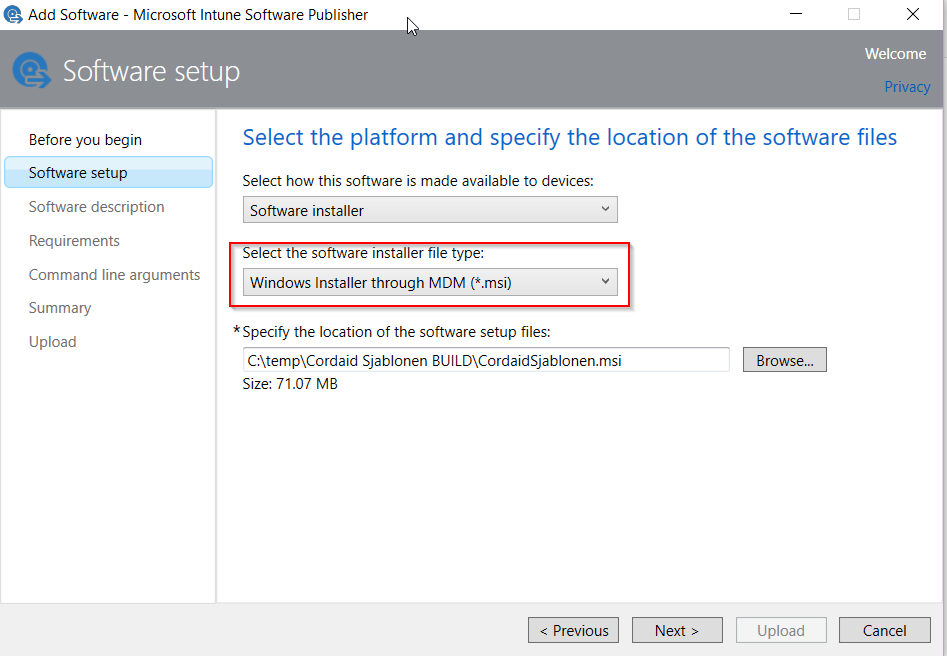
Ensure you have selected “Windows Installer through MDM”, the other methods won’t work.
Accept all other default settings or configure as you please and press Upload.
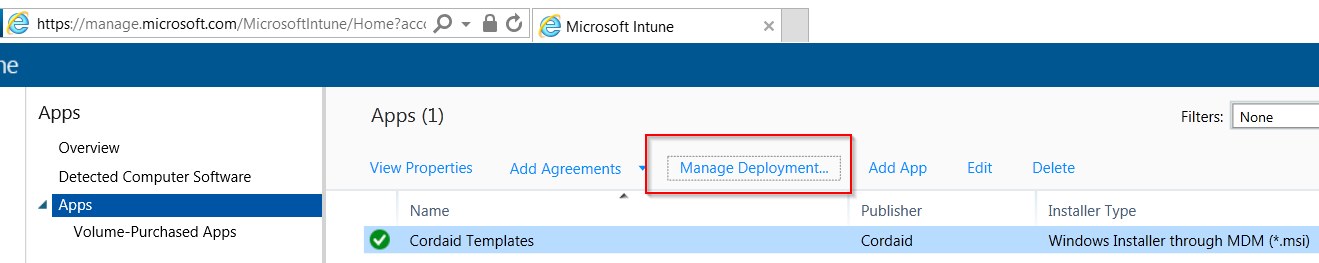
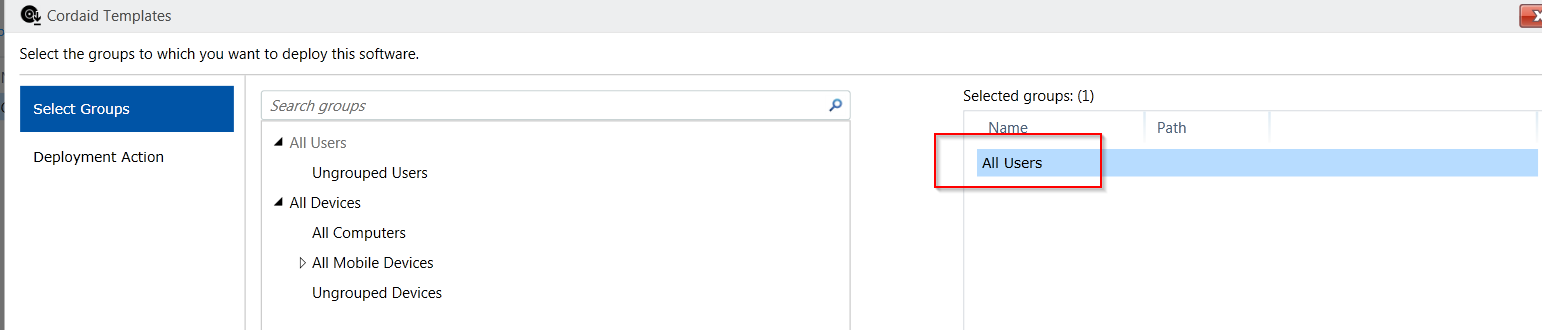
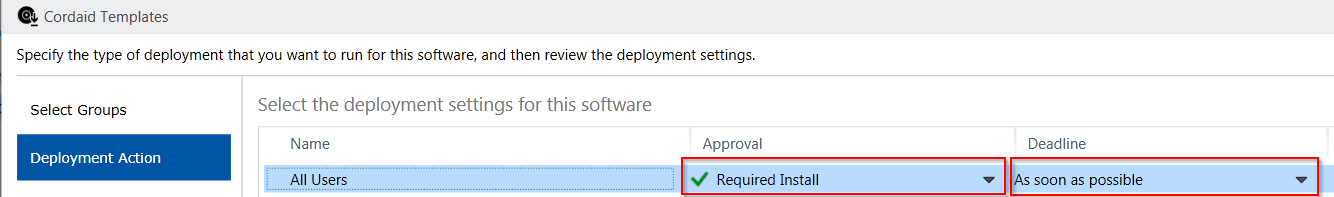
Once the upload completes, you’ll see the app in the Intune Console, but this won’t distribute the application yet, for that you’ll have to click ‘Manage Deployment” and configure a user based deployment:
And voila, within the hour your devices will have their templates deployed straight from Intune.
[…] A second case, comparable to EMS case: distributing Office templates and macro’s to your users on Windows 10 mobile managed…. […]